
Striking off the last row of your compliance to-do list isn’t the end of the road. The real work begins in maintaining this complex system and quickly implementing the regulatory changes required to stay compliant.
And this is where most companies hit a wall because compliance requires continuous strategic planning, budgeting, and attention to resources.
You can avoid most of the issues by treating GDPR compliant software management as an ongoing process, embedding accountability into daily operations, and replacing static documentation with dynamic visibility.
This guide outlines how to build such a system. Inside, you will learn what continuous compliance monitoring actually means in practical terms and receive a step-by-step roadmap to implement it without expanding your legal team.
Why does a one-time GDPR software compliance effort fail?
Achieving GDPR compliance once does not guarantee remaining compliant. Many organizations treat GDPR compliant software as a milestone project and consider the requirement satisfied.
However, achieving compliance is not a fixed process; it should remain an ongoing operational condition that aligns with constantly evolving systems and regulatory expectations. When governance remains static while infrastructure changes, the following gaps inevitably emerge:
- Data environments change. Organizations continuously introduce new technologies and integrations, which can alter how personal data is collected, processed, stored, or transferred.
- Shadow IT and decentralized data processing. Shadow IT is the term used to describe unsanctioned digital infrastructure that operates outside formal access controls. In practice, business units or organization staff often deploy tools without centralized visibility, leading to undocumented processing activities and increased risk exposure.
- Human error in manual documentation. Spreadsheet-based Records of Processing Activities (ROPA) management and manual control tracking inevitably result in incomplete records and outdated entries.
- Regulatory evolution and complexity. Authorities continuously refine expectations around accountability, transparency, DPIAs, security controls, vendor oversight, and data subject rights. This means that compliance management programs must be adaptive, as static documentation prepared at implementation quickly becomes outdated.
- Audit and enforcement intensity. Supervisory authorities are gradually moving away from reactive oversight and expect demonstrable, ongoing accountability rather than documentation assembled retroactively during investigations. This turns non-compliance into an operational and financial exposure.
- Static documentation vs dynamic infrastructure. While policies may remain unchanged for extended periods, system configurations and data flows can shift frequently, widening the gap between declared controls and operational reality.
- Audit & compliance fatigue. Repeated manual audit preparation and evidence gathering place continuous strain on legal and compliance teams. Over time, this creates broader compliance fatigue: obligations are perceived as recurring administrative disruption rather than embedded operational discipline. As fatigue increases, ownership becomes diffused, and GDPR for software controls degrade in quality, further widening the gap between documented compliance and actual practice.
Perhaps the most critical issue is that organizations assume they remain compliant simply because they once achieved compliance, even as their operational environment has materially changed, creating a false sense of security that will inevitably backfire.
What does continuous GDPR software monitoring actually mean?
Continuous GDPR software compliance monitoring is an operational model in which technical controls, documentation, vendor oversight, and risk assessments are automatically updated in response to real-time changes in the data environment.
| What it IS | What it ISN’T (and why) |
Systems and integrations are continuously scanned to detect new data flows and processing activities.
Changes in processing activities or system configurations trigger risk-scoring updates and, where necessary, DPIA requirements.
Technical and organizational controls are continuously checked against defined policies.
Identified issues generate structured tasks, assigned ownership, and tracked resolution timelines.
ROPA entries, DPIA records, and control evidence are automatically updated as operational changes occur. |
Periodic check-ins cannot detect risk introduced between review cycles and often rely on self-reporting.
Static documentation lacks version control integrity and integration with technical systems.
While legal oversight is critical, compliance cannot depend solely on retrospective policy interpretation without embedded operational controls. |
In short, continuous monitoring shifts GDPR compliant software development from a documentation-centered model to a systems-centered governance framework.
Core pillars of continuous compliance monitoring
If an organization looks to ensure GDPR in software development long-term, it should make a shift in its operational strategy, taking into account the following elements:
- Data visibility – Maintain real-time awareness of where personal data resides, how it flows, and which systems or vendors process it.
- Automated control testing – Continuously validate that technical and organizational safeguards function as intended, rather than relying on periodic manual verification.
- Risk scoring – Dynamically assess and update the risk profile of processing activities as systems, vendors, or data categories change.
- Workflow-based remediation – Convert detected gaps into structured, assigned tasks with tracked resolution and documented evidence.
- Audit-readiness by design – Ensure documentation, DPIAs, and control records are continuously updated and immediately retrievable for supervisory review.
Together, these pillars operationalize accountability and create the structural foundation for a continuously monitored GDPR compliance framework.
Regulatory expectations driving continuous monitoring of GDPR for employers
Understanding why continuous General Data Protection Regulation compliance monitoring is no longer optional starts with intent: the law and its compliance requirements were designed as an operational mandate requiring organizations to proactively identify, implement, and demonstrate compliance as an ongoing business practice.
Regulators now expect businesses to embed data protection into everyday operations and adapt to evolving risks in real time. The following principles are central to this shift.
Accountability principle (Article 5(2))
At the heart of the GDPR is the accountability principle, which requires organizations not only to comply with data protection principles but also to demonstrate that compliance continuously and credibly. Under Article 5(2), controllers must be able to produce evidence showing that processing adheres to GDPR software compliance principles such as lawfulness, purpose limitation, and data minimisation.
Operationally, this means you must implement measurable processes, retain verifiable records (e.g., processing logs, DPIAs), and show how controls operate in practice, rather than simply stating them in a policy. Accountability, therefore, demands continuous monitoring, because regulators will assess documented evidence of compliance at any given moment, not just during scheduled audits.
Data protection by design and by default (Article 25)
Article 25 requires organizations to integrate data protection principles into the design and operation of processing activities from the outset, and to configure systems so that only necessary personal data is processed by default.
This principle is a structural expectation, and continuous GDPR software compliance monitoring carries it out by ensuring that:
- changes in processing (new features, products, or integrations) are evaluated for privacy impact before deployment
- systems default to privacy-protective settings without manual intervention.
Data protection by design and by default shifts compliance from reactive fixes to built-in safeguards, meaning ongoing reviews of architecture and configuration are part of how GDPR compliance is demonstrated.
Ongoing risk assessment (Articles 24 & 32)
Article 24 establishes a general obligation to implement appropriate technical and organisational measures to demonstrate compliance with processing principles.
Article 32 specifically requires controllers and processors to ensure security of processing using risk-based safeguards, from encryption to restore-and-resume capabilities after failures.
These provisions carry several operational implications:
- Security controls must be continuously tested, not simply validated once.
- New processing activities must trigger updated risk analysis.
- Risk-based decisions must be documented and defensible.
In practice, this means ongoing risk scoring and control evaluation. Trigger-based DPIAs, automated security checks, and integrated workflows for remediation help translate risk assessment mandates into living operational processes.
Enforcement trends
Regulatory enforcement of the GDPR compliance for businesses is both active and evolving. Recent data shows European authorities remain aggressive in penalties and oversight, often focusing on areas where complacency tends to emerge: inadequate organisational and technical measures, poor documentation, and failure to demonstrate compliance. In 2025 alone, EU regulators issued over €1.2 billion in GDPR fines across sectors as breach notifications surged.
A few key enforcement trends illustrate why continuous monitoring is becoming an expectation rather than a best practice:
- Higher frequency and broader scope of fines. Regulators are targeting procedural gaps, as well as and substantive security lapses. Penalty totals continue to rise year over year, with a growing share tied to inadequate measures under Articles 24 and 32.
- Focus on emerging technologies. Supervisory authorities are scrutinising how advanced systems handle personal data, particularly where profiling, automated decisions, or large-scale data processing occur. For example, AI systems that involve personal data processing without sufficient transparency, risk management, and governance are receiving special attention.
- Demand for real-time proof of compliance. Rather than accepting post-hoc remediation plans, regulators increasingly expect businesses to show current, up-to-date evidence of controls and risk management. Static reports are no longer sufficient; documentation must reflect actual, ongoing conditions.
- Data subject rights and response times. Enforcement is also emphasising timely responses to access requests, rectification, or deletion, pushing organisations to adopt systems that can track and demonstrate compliance with rights management as processes evolve.
These regulatory expectations and enforcement behaviours make clear that episodic GDPR software compliance reviews are inadequate. Accountability, privacy-by-design, and ongoing risk assessment principles explicitly demand operational integration and demonstrable consistency: outcomes that can only be achieved through continuous GDPR monitoring.
Building a continuous GDPR compliance software framework: 4 core components
Quantumrun’s SaaS Industry Growth report shows that 99% of organizations use at least one SaaS tool. Such universal adoption of technologies that store and process personal data highlights the demand for GDPR-compliant software development.
Moreover, continuous monitoring should be built into how your organization discovers data, detects risk, validates controls, and coordinates remediation to ensure it works. In practice, that means designing a framework around four components that map directly to what regulators care about: ongoing visibility, risk-based controls, accountable execution, and demonstrable oversight.
#1 Centralize data visibility
Why it matters: You can’t monitor compliance you can’t see. Automated data mapping turns low-effort documentation into continuous system-of-record accuracy, reducing blind spots in ROPA, data flow maps, and system inventories.
- Continuous scanning of systems: Regular discovery across cloud storage, SaaS, endpoints, and databases identifies where personal data exists and where new processing may have emerged.
- Tracking data flows: Mapping how data moves between systems enables you to detect unapproved processing paths and supports transfer impact workflows.
- Identifying personal data categories: Classification distinguishes personal data types, and flags special categories where monitoring thresholds should be stricter (e.g., health data).
This component aligns with regulator expectations that processing documentation must stay current and should be updated as necessary to reflect reality.
#2: Define risk thresholds
Why it matters: General Data Protection Regulation compliance is risk-based by design. Real-time risk detection ensures your program reacts when processing changes push an activity into a higher-risk category—before an incident, a complaint, or a regulator forces that discovery.
- DPIA triggers: Automatically flag events that should initiate or refresh a DPIA, such as introducing a new profiling model, expanding processing scale, adding a new sensitive data category, or deploying a new AI-driven decision workflow.
- Cross-border transfer alerts: Detect transfers to third countries and trigger safeguards workflows (SCC verification, technical controls, and vendor commitments).
- Retention policy violations: Identify data stored beyond defined retention periods, orphaned datasets, or duplicated repositories, and route remediation actions to owners.
Risk detection is not only about privacy; it’s inseparable from the impact of breaches. IBM’s 2025 Cost of a Data Breach report puts the global average cost of a data breach at USD 4.4 million, reinforcing the economic case for catching risk early rather than paying for remediation late.
#3 Automate remediation workflows
Why it matters: This component closes the gap between documented intent and operational reality by continuously validating control performance and ensuring issues become owned, tracked, and resolved.
- Access control validation: Monitor whether access aligns with least privilege and flag deviations that could expose to GDPR Article 32.
- Breach detection triggers: Integrate security signals to quickly activate privacy impact evaluation and automatically capture evidence.
- Automated task routing to DPO/IT: Convert compliance findings into workflow tickets with a defined owner, SLA, escalation path, and evidence capture, so that remediation becomes measurable and auditable rather than ad hoc.
This is where GDPR compliant software development becomes real: not a dashboard, but a closed-loop system that takes a signal and produces a documented outcome.
How to implement a continuous GDPR-compliant software monitoring framework in 5 steps?
Building a GDPR software compliance monitoring framework is a process of engineering a system where visibility, risk detection, control validation, and accountability operate in a closed loop. The following five steps provide a practical implementation roadmap that organizations can follow without turning compliance into an isolated legal project.
Step 1: Centralize data visibility
Ongoing compliance begins with visibility. Without a consolidated view of where personal data resides, how it moves, and who can access it, continuous monitoring is impossible. Centralization eliminates fragmented oversight and reduces blind spots.
Start by integrating key systems into a single compliance layer:
- CRM systems that store customer and prospect data.
- HRIS platforms that manage employee information.
- Cloud storage and collaboration tools, where unstructured personal data often accumulates.
- Additional SaaS tools that process marketing, support, finance, or operational data.
System integration allows automated discovery and mapping of personal data across environments. This replaces static documentation with dynamic system awareness.
Equally important is eliminating spreadsheet-based tracking for ROPA, DPIAs, vendor logs, and retention lists. Spreadsheets create version conflicts, ownership confusion, and delayed updates. A centralized platform ensures documentation updates reflect real operational changes rather than periodic manual revisions.
Step 2: Define risk thresholds
Visibility alone does not ensure GDPR in software development; it must be tied to structured risk logic. Defining risk thresholds allows organizations to automatically identify when a processing activity requires escalation or additional safeguards.
High-risk processing triggers should be clearly defined. These may include:
- Introduction of new profiling or automated decision-making.
- Processing of large volumes of personal data.
- Expansion into special categories of data (health, biometrics, ethnicity).
- New cross-border transfers.
- Deployment of AI-driven systems that impact individuals.
Sensitive data classification rules should also be codified. By assigning higher monitoring weight to special category data, financial data, or employee records, the organization ensures that risk scoring dynamically reflects regulatory exposure.
Step 3: Automate control checks
Continuous compliance requires ongoing validation that safeguards are functioning as designed. Automated control checks ensure that policies are not merely written — they are actively enforced.
Key control areas include:
- Retention management – Automatically detect data exceeding retention periods and trigger deletion workflows or owner review.
- Access log validation – Monitor access rights and flag excessive permissions, dormant accounts, or privilege escalations.
- Cross-border flow monitoring – Identify transfers or remote access patterns that may constitute international data transfers and require safeguards.
Automated validation closes the gap between declared policy and technical reality. Instead of discovering non-compliance during audits, organizations detect deviations as they occur. This aligns directly with GDPR’s risk-based security expectations under Articles 24 and 32.
Step 4: Build alert-to-resolution workflows
Monitoring generates signals. Without structured remediation, those signals become noise. Building alert-to-resolution workflows ensures every compliance finding results in documented action.
Effective workflow design includes:
- Assigned ownership – Each issue must have a clearly defined responsible role (e.g., IT, Risk, DPO).
- Tracked remediation SLAs – Define acceptable resolution timelines and escalation procedures.
- Audit trail preservation – Capture decisions, evidence uploads, timestamps, and confirmation of closure.
This step transforms GDPR for companies from reactive firefighting into controlled operational management. Alerts related to retention violations, unauthorized access, or vendor changes automatically generate measurable, reportable tasks.
Over time, workflow data also provides insight into systemic weaknesses — for example, recurring retention issues may signal process gaps in certain departments.
Step 5: Continuously report to stakeholders
Sustainable compliance requires transparency at multiple organizational levels. Continuous reporting ensures that governance is not siloed within compliance teams but integrated into strategic oversight.
Reporting mechanisms should include:
- Executive dashboards presenting high-level compliance posture, risk exposure trends, and remediation performance.
- Compliance KPIs, such as time to DPIA completion, percentage of systems mapped, vendor reassessment frequency, and SLA adherence.
- Centralized evidence repositories where documentation, control logs, and remediation records are stored and easily retrievable.
- Organizational shifts, including regular risk committee reviews and compliance updates integrated into board reporting cycles.
Continuous reporting shifts GDPR compliance for businesses from episodic audit preparation to ongoing governance. Organizations can demonstrate structured oversight rather than scrambling to reconstruct documentation during regulator inquiries.
At this stage, the compliance framework moves from implementation into operational maturity.
In another guide, we also explore the necessary checks and fixes to achieve GDPR compliance for websites. Take a look!
RACI model for compliance governance and stakeholder engagement
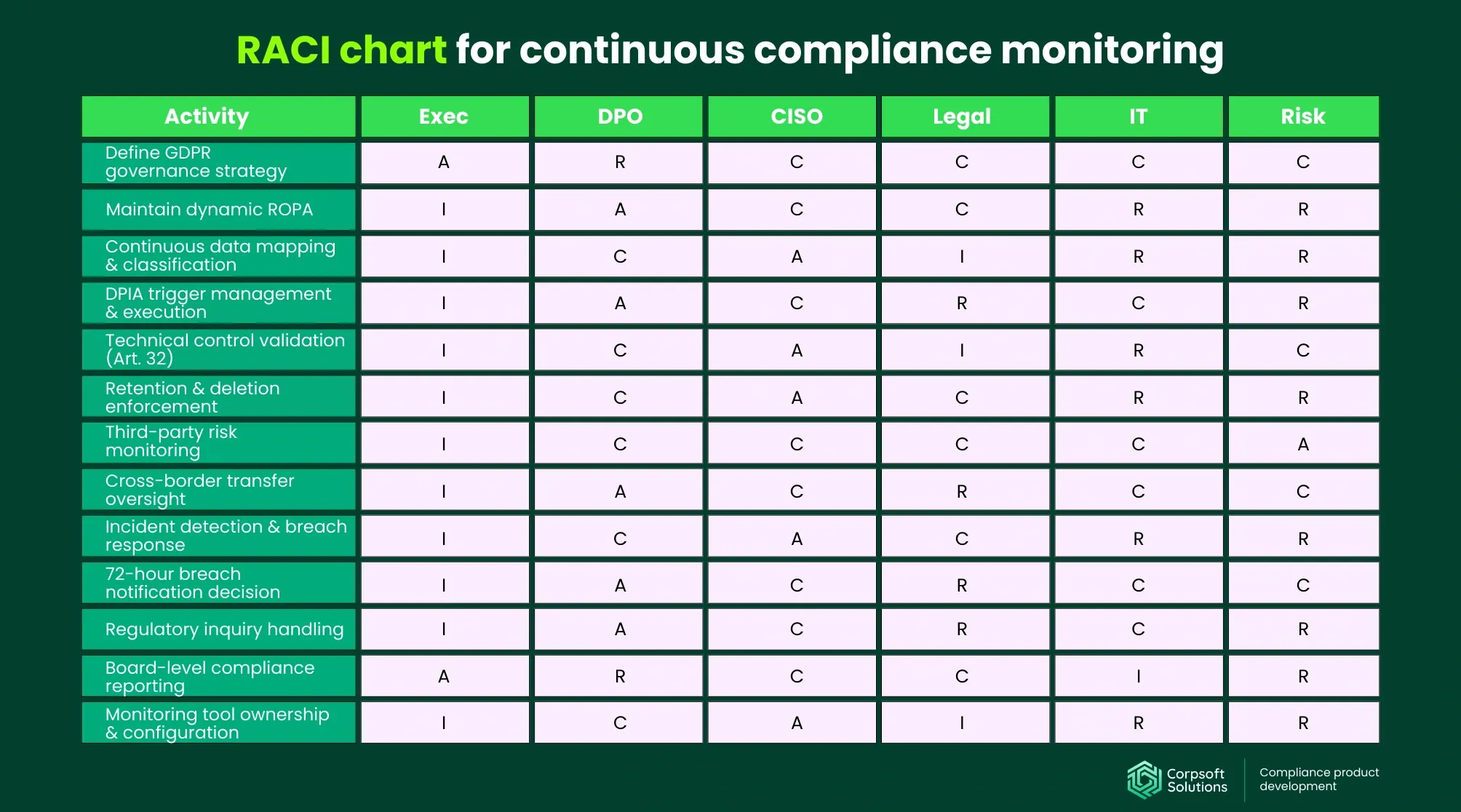
A RACI model is a governance tool that clarifies who is Responsible (R), accountable (A), consulted (C), and informed (I) for each compliance activity. In a continuous GDPR software compliance framework, clearly defined roles prevent duplication, gaps, and ownership disputes.
- Responsible – The role that executes the task (e.g., IT validating access controls).
- Accountable – The role ultimately answerable for the outcome (e.g., DPO for GDPR integrity).
- Consulted – Stakeholders whose input is required before action.
- Informed – Parties kept updated on progress or outcomes.
A well-designed RACI model ensures that continuous monitoring does not become a fragmented effort. It embeds compliance into operational structures, reinforces accountability, and supports defensibility during regulatory scrutiny.
How can continuous monitoring reduce the long-term costs of GDPR for US businesses?
Continuous GDPR software compliance monitoring with technology access and tracking controls, risk detection, and real-time automation of documentation improves the regulatory posture, reduces long-term costs, and delivers measurable business value. 73% of organizations that adopted automated governance tools report significant cost savings across audit preparation, legal overhead, and operational inefficiencies compared to manually driven compliance programs.
To quantify the value of continuous monitoring, it’s essential to track metrics that demonstrate progress, efficiency, and risk reduction. These KPIs not only measure performance but also translate into real cost savings.
Key KPIs for the compliance monitoring system
| KPI | Definition | How is it measured? | Business impact |
| % of systems mapped | The proportion of your data ecosystem (CRM, HRIS, cloud storage, apps) that is actively discovered and inventoried. | (Number of systems integrated / Total systems in environment) × 100. | Higher coverage means fewer blind spots, reducing unexpected risk and downstream remediation costs. |
| Time to risk detection | The average time between a change in processing or configuration and when a risk-relevant alert is generated. | Average time (hours/days) from event to alert across risk types. | Faster detection prevents compliance gaps from escalating into breaches. |
| DPIA completion cycle time | The time from identifying the need for a DPIA to its formal completion. | Average days from DPIA trigger to approved documentation | Automated workflows shrink this cycle and improve accuracy, reducing delays that can slow projects. |
| Vendor risk update frequency | How often are third-party risk profiles reassessed? | Number of vendor reassessments per year / Total vendors. | Frequent updates prevent outdated risk assumptions. Manual vendor reviews can take hours per assessment, but automation reduces them, freeing staff time. |
| Time to evidence retrieval | Time taken to locate and present evidence for a control, audit request, or regulator inquiry. | Average minutes or hours per retrieval request. | Automated evidence reduces ad-hoc search time, significantly lowering audit preparation hours. |
| Breach response readiness metrics | Metrics such as time to detect, time to contain, and time to notify after a potential breach event. | Average hours/days from initial signal to regulator-aligned notification. | Faster response reduces financial and reputational impact. Organizations that use real-time monitoring can significantly reduce the cost impact of security incidents. |
| Compliance velocity | The overall speed at which compliance tasks (policy updates, control validations, reports) are completed. | Composite score of cycle times across core tasks. | Higher velocity drives operational efficiency and lowers total cost of compliance. |
Tracking these KPIs establishes a performance baseline and highlights areas where automation yields the greatest financial impact.
Translating compliance into business impact
Beyond compliance itself, monitoring yields measurable business value. Each impact below can be linked to industry benchmarks or research findings.
- Reduced audit preparation time. Companies using automated monitoring typically see audit prep times cut by up to 60%, meaning weeks of staff work saved annually, which translates directly into labor cost savings and lower external audit fees.
- Reduced regulatory exposure. Continuous controls and automated risk detection help organizations avoid violations altogether. For example, the adoption of fraud-prevention algorithms and workflow automation in the financial sector helped reduce operational costs by $3.2 million per year and achieve an 85% reduction in manual review requirements.
- Lower legal review hours. The Hyperproof 2026 IT Risk and Compliance Benchmark Report states that 56% of respondents use a common controls framework to streamline their GRC processes. Shifting toward a repeatable method for handling differences across their businesses without turning compliance into a series of one-off interpretations and exceptions helps reduce legal overhead and free staff time for implementation.
- Improved procurement speed. Standardized vendor risk profiles and documented safeguards shorten procurement review cycles. Organizations that use automation tools to simplify the vendor risk assessment process can onboard partners 65% faster without additional risk, yielding direct operational efficiency.
- Higher customer trust in B2B sales. In regulated markets, customers expect robust compliance postures. Automated compliance and audit readiness increase bid success rates in procurement that requires SOC 2, ISO 27001, or GDPR assurance.
Manual vs automated compliance governance: a demonstration of business impact
To illustrate the cost impact, consider a modeled mid-sized organization with 150 SaaS systems and 80 vendors:
| Cost area | Manual governance cost per year | Continuous automated monitoring cost per year | Estimated savings / Impact |
| Compliance FTE labor | €170k–€420k | €60k–€180k (reduced admin load) | €80k–€240k |
| Vendor risk reviews | €25k–€170k | €10k–€80k | €15k–€90k |
| Audit preparation & evidence reconstruction | €30k–€120k | €5k–€25k | €15k–€95k |
| External legal review hours | €8k–€90k | €2k–€36k | €6k–€54k |
| Monitoring & tooling costs | Minimal (spreadsheets/manual) | €30k–€180k | Predictable cost replacing labor overhead |
| Implementation (one-time) | N/A | €20k–€150k (one-time) | Operational efficiency investment |
| Expected-value incident exposure | €12.5k–€300k | Reduced probability/severity | Risk-adjusted savings variable |
| Procurement & due diligence delays | €10k–€75k (labor + opportunity cost) | Significantly reduced | Faster deal cycles |
| Revenue trust uplift (modeled) | Indirect | 1–3% win-rate improvement potential | Revenue impact varies by ACV |
To illustrate the cost impact, consider a modeled mid-sized organization with 150 SaaS systems and 80 vendors. The financial equation becomes clear: while continuous GDPR compliance software requires an investment, it replaces recurring manual costs, reduces the probability of regulatory exposure, and enhances operational efficiency.
Common implementation pitfalls of GDPR for businesses
Implementing continuous GDPR monitoring can significantly improve governance maturity, but only if it is executed strategically. Many organizations undermine their own initiatives by misjudging scope, ownership, or operational alignment. The following pitfalls are common in early-stage implementations and often explain why compliance automation efforts stall or fail to deliver measurable ROI.
- Over-automation without governance. Deploying tools without clearly defined risk thresholds or ownership models leads to alert fatigue and unresolved findings. Effective implementation requires governance first: defined risk appetite, DPIA triggers, retention standards, and RACI alignment. Automation should operationalize policy, not substitute for it.
- Tool overload. Organizations often layer multiple point solutions, such as data discovery tools, vendor risk platforms, and ticketing systems. However, each additional tool increases integration complexity and administrative overhead, undermining the very objective of continuous monitoring. A consolidated architecture with interoperable systems reduces friction and ensures that alerts, evidence, and workflows remain synchronized.
- Lack of executive sponsorship. Without executive accountability, initiatives become underfunded or deprioritized when competing business objectives arise. When leadership frames monitoring as a strategic risk-management function rather than a regulatory burden, organizational adoption accelerates.
- Treating monitoring as a purely IT problem. GDPR software compliance encompasses lawful-basis management, purpose limitation, vendor oversight, and data-subject rights. Effective programs operate cross-functionally, combining DPO oversight, legal input, IT implementation, and risk monitoring. Limiting ownership to IT reduces regulatory defensibility and creates blind spots in non-technical processing activities.
- Ignoring the vendor ecosystem. Vendors, subprocessors, cloud providers, and SaaS integrations continuously change their security posture, data residency models, and contractual terms. Without structured third-party monitoring, organizations may unknowingly expand cross-border transfers or sensitive processing activities. Continuous oversight must extend beyond internal systems to include DPA tracking, transfer safeguards, and risk re-scoring when vendor conditions change.
Avoiding these pitfalls requires a balanced approach: governance before automation, integration over fragmentation, executive oversight, cross-functional ownership, and ecosystem-wide visibility.
When is it time to move beyond manual GDPR-compliant software tracking?
Even the best executed strategy for achieving GDPR compliance for businesses eventually reaches a point where manual processes, periodic reviews, and fragmented oversight can no longer keep pace with operational change.
Recognizing that the tipping point is critical. Continuous monitoring is not necessary for every organization at the same maturity stage, but certain structural indicators signal that static governance models are no longer sufficient.
You likely need continuous monitoring if:
- You operate in multiple EU markets and must manage varying supervisory expectations, cross-border transfers, and jurisdiction-specific risk exposure.
- You process sensitive categories of data (health, biometric, financial, employee records), where risk thresholds are lower, and DPIA triggers are more frequent.
- You manage more than 20 vendors or subcontractors, increasing third-party exposure and the complexity of contractual oversight.
- Your last audit required manual document reconstruction, involving spreadsheets, scattered evidence, and significant internal coordination.
- Compliance tasks regularly compete with core business priorities, causing delayed updates to ROPA, DPIAs, or vendor reviews.
- New SaaS tools are introduced faster than governance processes can evaluate them, creating undocumented data flows.
If these signals resonate, manual tracking is no longer sustainable — and the cost of inaction grows with every system change.
Why you should choose Corpsoft Solutions as your trusted partner for developing GDPR compliance?
Corpsoft Solutions specializes in building long-term compliance solutions, helping you move from reactive documentation to structured, continuous GDPR monitoring designed for operational resilience, scalability, and audit readiness.
We deliver this through a combination of strategic expertise and technology-enabled execution:
- Cutting-edge expertise rooted in real-life cases and experience. Corpsoft Solutions’ methodology is shaped by practical experience with regulatory reviews, DPIA challenges, cross-border transfer assessments, and supervisory authority expectations. This allows us to design monitoring frameworks that are compliant and defensible under scrutiny. We understand how regulators interpret accountability, how enforcement actions unfold, and where organizations most commonly fail — and we build safeguards accordingly.
- Use of automation tools, AI agents, and advanced technologies vetted against current GDPR requirements. We deploy carefully selected compliance automation platforms, AI-driven data discovery tools, and workflow orchestration systems that align with Articles 5, 24, 25, and 32. Each technology component is evaluated for lawful processing logic, transparency, logging capabilities, and risk-based safeguards.
- Custom solutions aligned with your business goals and European market strategy. Rather than imposing a generic compliance template, we architect tailored monitoring frameworks that reflect your operational model, data ecosystem, vendor network, and product roadmap. This ensures that compliance becomes an enabler of growth, helping you shorten time to market in Europe by embedding DPIA triggers, transfer safeguards, and retention controls directly into product development and procurement workflows.
- Ongoing support to protect your reputation before European regulators. We provide continuous optimization, tracking of regulatory updates, risk reassessment, and governance refinement to ensure your program evolves alongside enforcement trends. This sustained partnership helps preserve your credibility, strengthen customer trust, and maintain an unblemished compliance record in the eyes of supervisory authorities.
Conclusion
Continuous GDPR compliance is an operational capability that must evolve alongside your technology stack, vendor ecosystem, and regulatory landscape.
Organizations that embed monitoring, automation, and clear governance into their daily workflows not only reduce risk but also gain measurable efficiency and strategic flexibility. By shifting from reactive documentation to continuous oversight, compliance becomes a driver of trust, speed, and resilience. The sooner this transition is made, the stronger and more defensible your European market position becomes.
Subscribe to our blog


